Configure Ubuquiti Edge Router VPN with SonicWall
How to Setup a VPN between Ubiquiti Edge Router and SonicWall Devices
I just spent all day trying to setup a new VPN connection between a Ubiquiti Edge Router Light (ERL) and a SonicWALL TZ210. While there are several articles and blogs out there which pointed me in the right direction, I still encountered issues. I wanted to jot down my notes before I forget them.
I started off by following a now deleted wiki article from Ubiquiti’s wiki site. In this example, I will use the following IP Address
Local Site Public IP: 1.1.1.1
Local Site Private IP: 192.168.1.0/24
Remote Site Public IP: 2.2.2.2
Remote Site Private IP: 10.10.1.0/24Ubiquiti ERL Configuration – Local Site
ubnt@ubnt:~$ configure
[edit]
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN compression disabled
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN lifetime 3600
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN mode tunnel
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN pfs disable
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN proposal 1
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN proposal 1 encryption aes128
ubnt@ubnt# set vpn ipsec esp-group ESPSonicWallVPN proposal 1 hash sha1
ubnt@ubnt# set vpn ipsec ike-group IKESonicWallVPN
ubnt@ubnt# set vpn ipsec ike-group IKESonicWallVPN lifetime 28800
ubnt@ubnt# set vpn ipsec ike-group IKESonicWallVPN proposal 1
ubnt@ubnt# set vpn ipsec ike-group IKESonicWallVPN proposal 1 dh-group 2
ubnt@ubnt# set vpn ipsec ike-group IKESonicWallVPN proposal 1 encryption aes128
ubnt@ubnt# set vpn ipsec ike-group IKESonicWallVPN proposal 1 hash sha1
ubnt@ubnt# set vpn ipsec ipsec-interfaces interface eth0
ubnt@ubnt# set vpn ipsec logging log-modes all
ubnt@ubnt# set vpn ipsec logging log-modes control
ubnt@ubnt# set vpn ipsec nat-traversal enable
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 local-address 1.1.1.1
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 authentication mode pre-shared-secret
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 authentication pre-shared-secret mysecretvpnkey1010
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 connection-type initiate
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 default-esp-group ESPSonicWallVPN
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 ike-group IKESonicWallVPN
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 tunnel 1
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 tunnel 1 allow-nat-networks disable
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 tunnel 1 allow-public-networks disable
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 tunnel 1 esp-group ESPSonicWallVPN
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 tunnel 1 local prefix 192.168.1.0/24
ubnt@ubnt# set vpn ipsec site-to-site peer 2.2.2.2 tunnel 1 remote prefix 10.10.1.0/24
ubnt@ubnt# commit
ubnt@ubnt# save
ubnt@ubnt# quitSonicWall Configuration Log into the web management of your SonicWall device and click VPN, then click “Add…”
General
Policy Type: Site to Site
Authentication Method: IKE using Preshared Secret
Name: Any name you want
IPsec Primary Gateway Name or Address: Public IP of your Ubiquiti
IPsec Secondary Gateway Name or Address: Blank
Shared Secret: mysecretvpnkey1010
Confirm Shared Secret: mysecretvpnkey1010
Local IKE ID: IP Address – Public IP Of your SonicWall
Peer IKE ID: IP Address – Public IP Of your Ubiquiti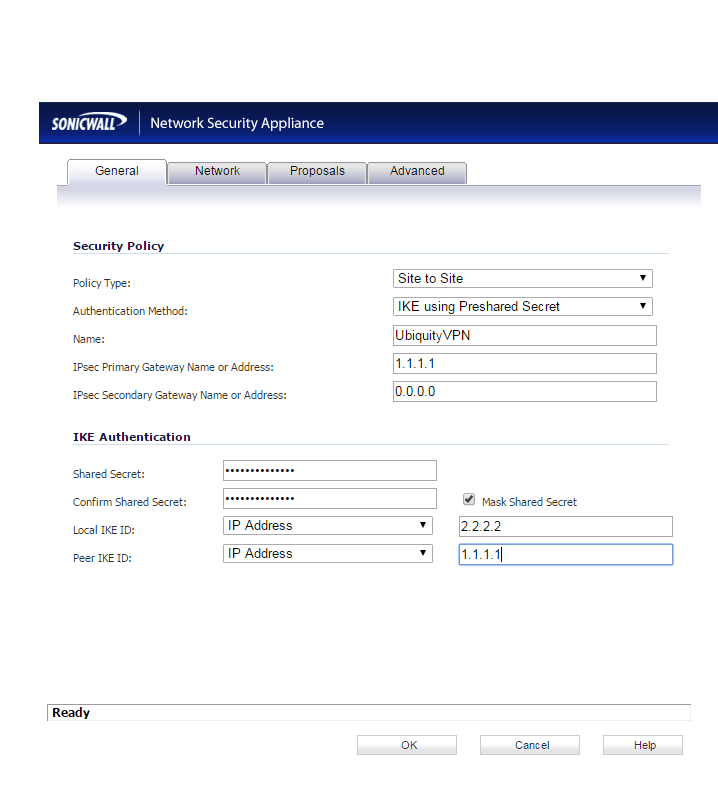
Network
Choose local network form list: Firewalled Subnets
Choose destination network from list: Ubiquity LAN Network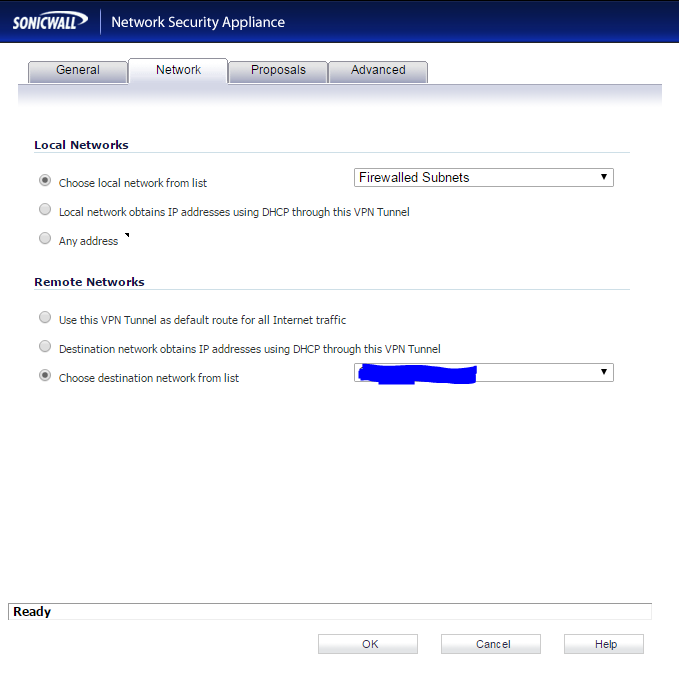
Proposals
Ike (Phase 1) Proposal
Exchange: Main Mode
DH Group: Group 2
Encryption: AES-128
Authentication: SHA1
Lime Time (seconds): 28800
Ike (Phase 2) Proposal
Protocol: ESP
Encryption: AES-128
Authentication: SHA1
Uncheck Perfect Forward Secrecy
Life Time (seconds): 3600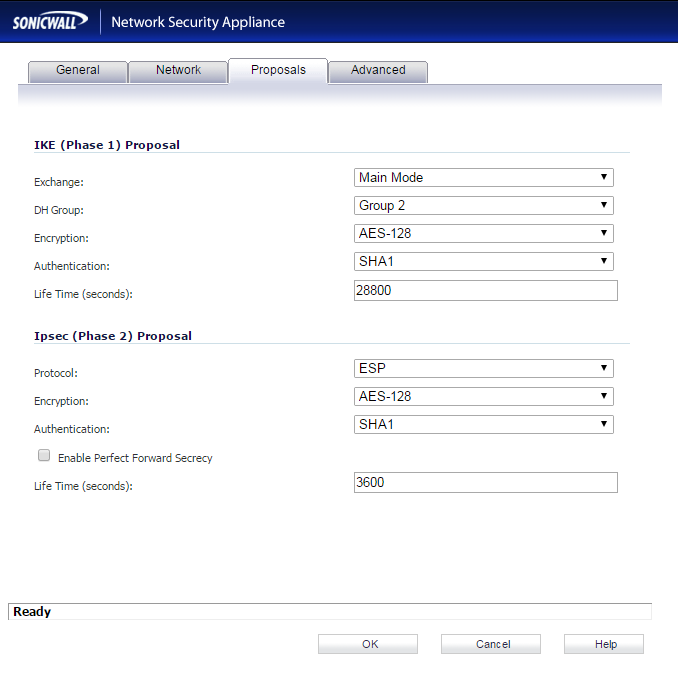
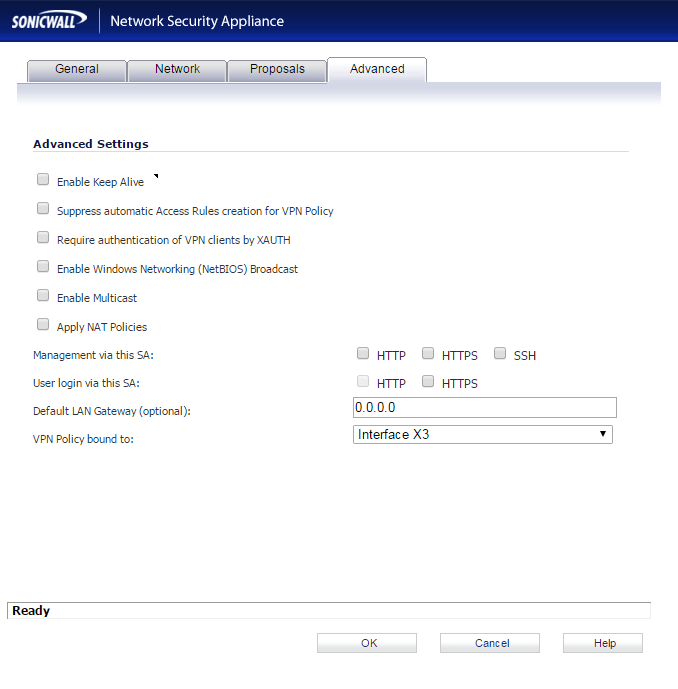
Advanced Leave everything unchecked and set the VPN Policy Bound to dropdown to your WAN interface name
Troubleshooting After configuring both devices, I saw that the tunnel came online but was not passing any traffic. After hours of playing around, I finally found the setting in the Ubiquiti device.
Log into the Ubiquiti through the web portal (default username is ubnt, default password is ubnt) Click the “Config Tree” menu item in the top right In the left menu tree, expand “vpn->ipsec” The “auto-update” field was blank on my device. After entering 3600 in the field and saving the config, data started to flow.
